Notify to users about changes made to their authenticators
Introduction
This feature enables the system to send notification emails to users when changes are made to their authenticators. Additionally, it fires an event to a service bus when configured, allowing external services to be notified of the changes as well. This helps to keep users informed and ensures seamless communication between the system and external services.
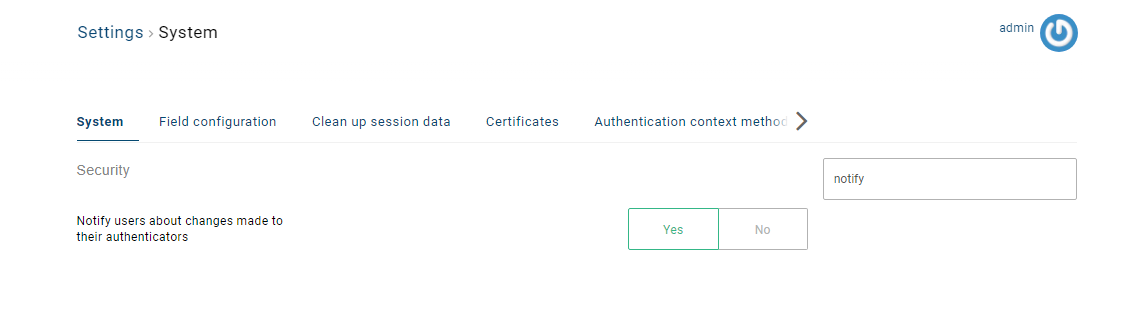
To enable this feature, navigate to the Security section in the Settings and set Notify users about changes made to their authenticators to Yes.
In this version, the supported authenticators are password, TOTP, WebAuthn, and Device Authentication (Trusted Browser). Other authenticators, such as OS2faktor, Email, and SMS, will be supported in the future.
Notification via email
Configuration
To enable email notifications for your user accounts in Safewhere Identify, follow these steps:
Configure the email server. You can find it in the following link.
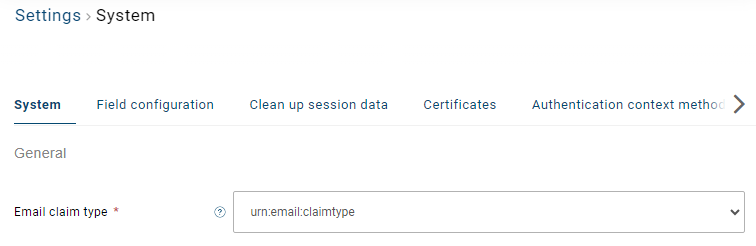
Set up the email claim type in the Settings > System.
Modify email templates
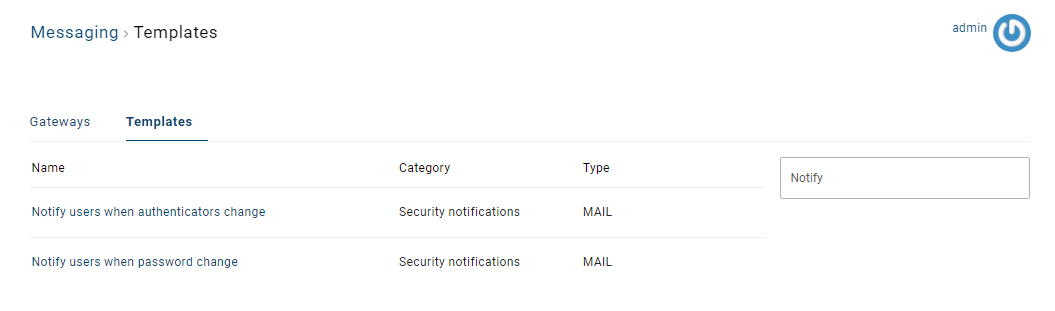
We have introduced two new email templates as described below:
Notify users when authenticators change: This new email template is designed to notify users when there are changes made to their authenticators, such as adding, removing and changing authenticators from their account.
Notify users when password change: This new email template is used to inform users when their passwords have been changed.
You can modify these email templates in Messaging > Templates.
You can find explanations for both email templates in the following link.
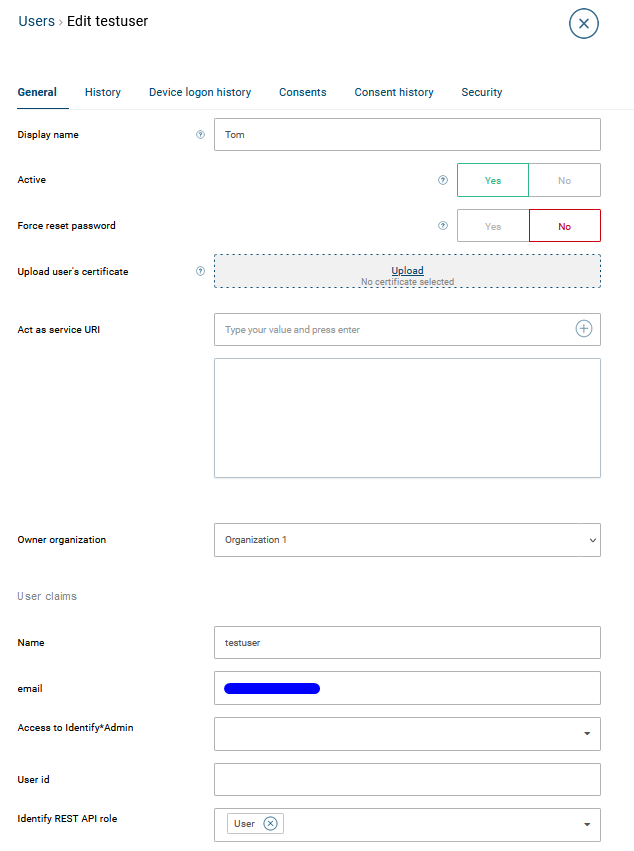
Indeed, users need email addresses to receive change notifications.
Use cases
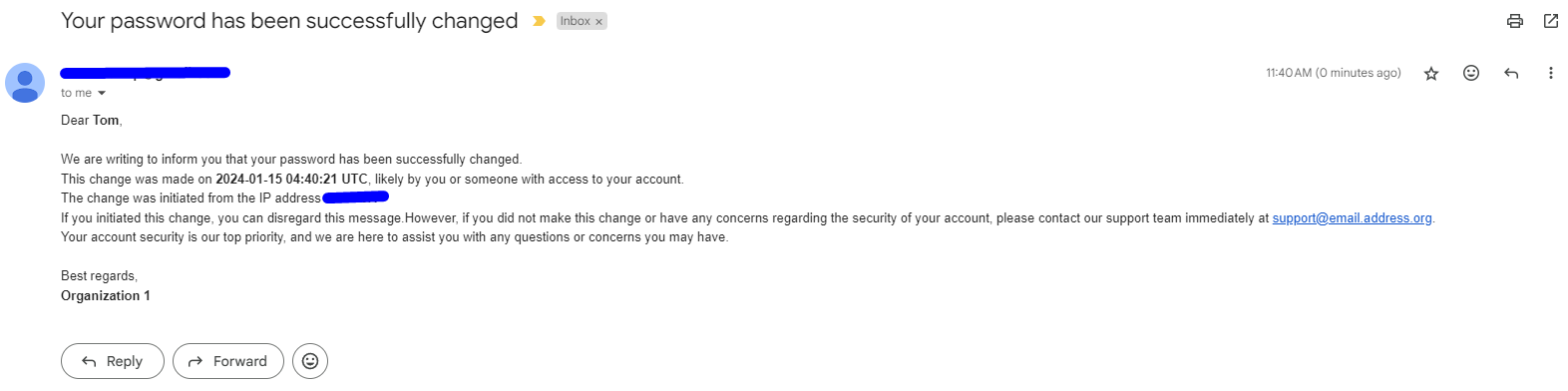
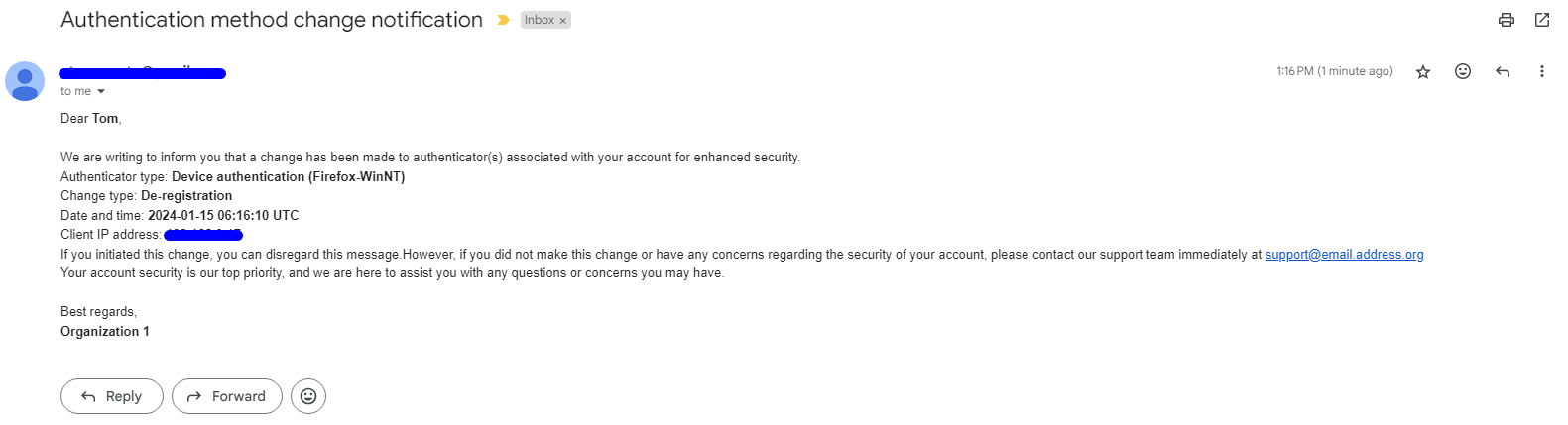
When a user changes their password or an administrator changes it for them, a notification email will be sent to their mailbox.
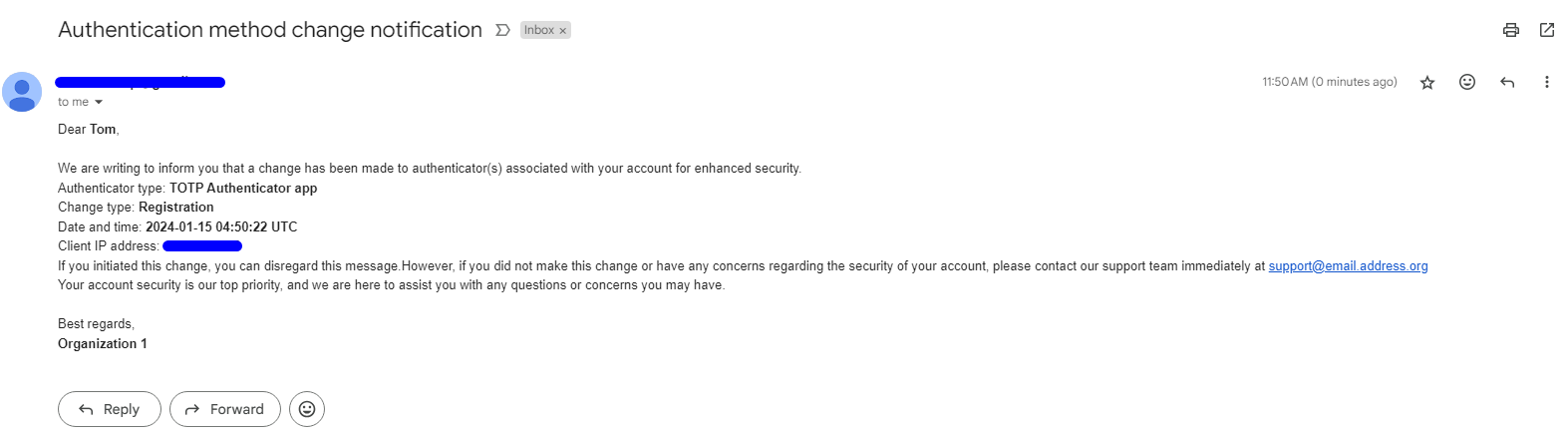
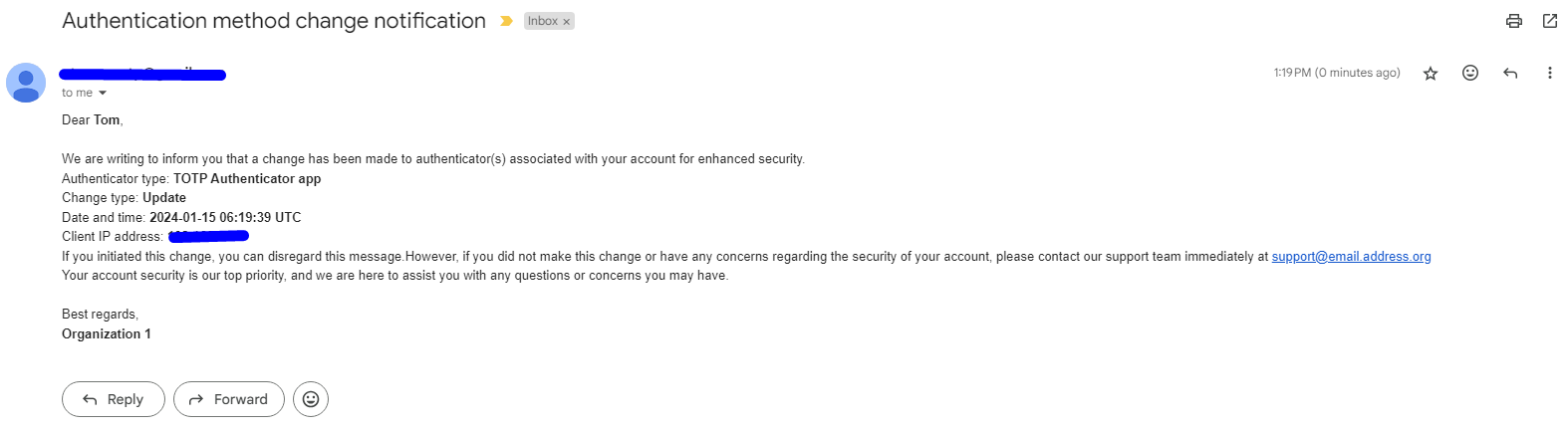
When a user registers a TOTP Authenticator, a notification email will be sent to their mailbox.
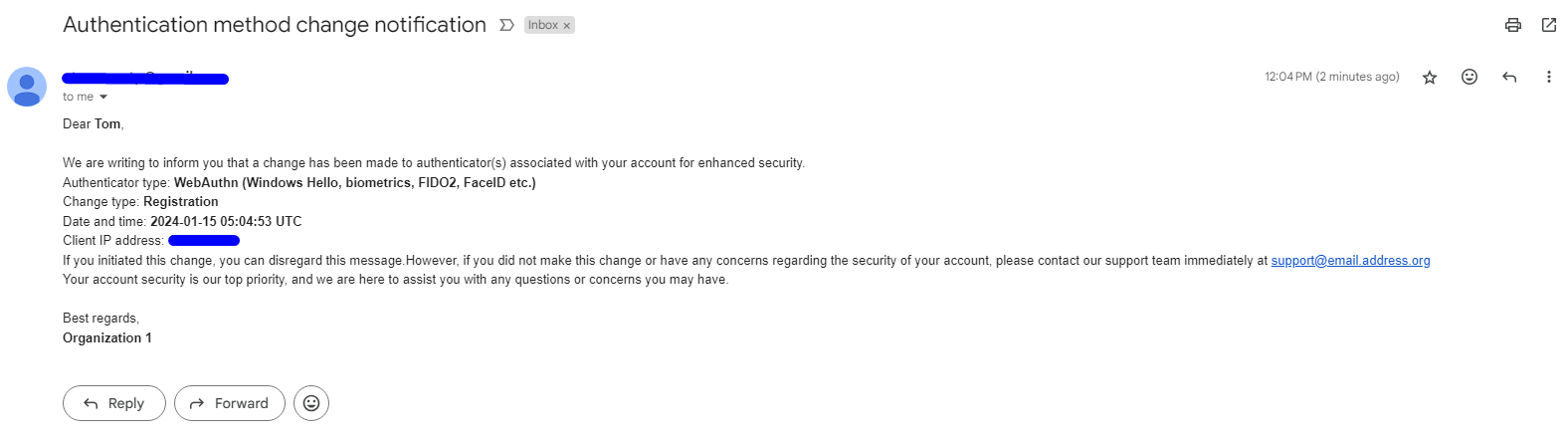
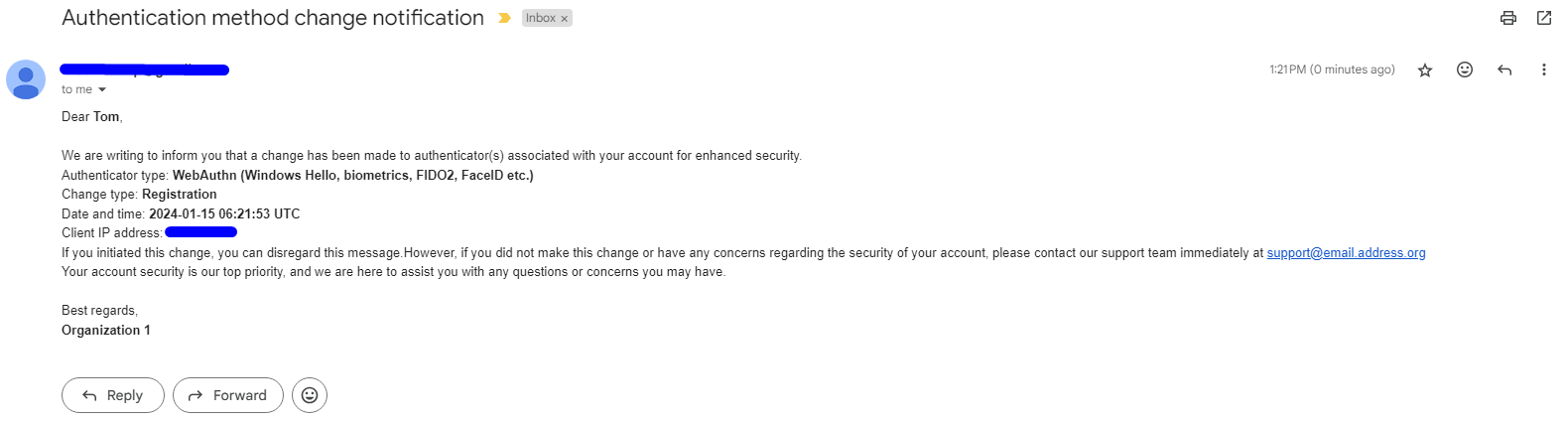
When a user registers a WebAuthn, a notification email will be sent to their mailbox.
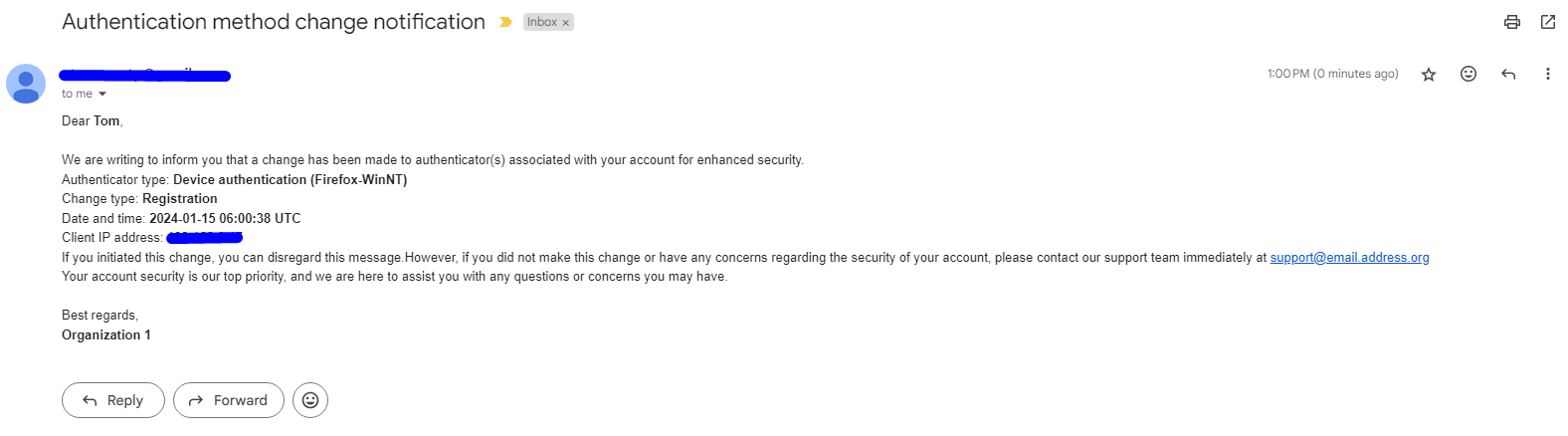
When a user registers a Device Registration (Trusted Browser), a notification email will be sent to their mailbox.
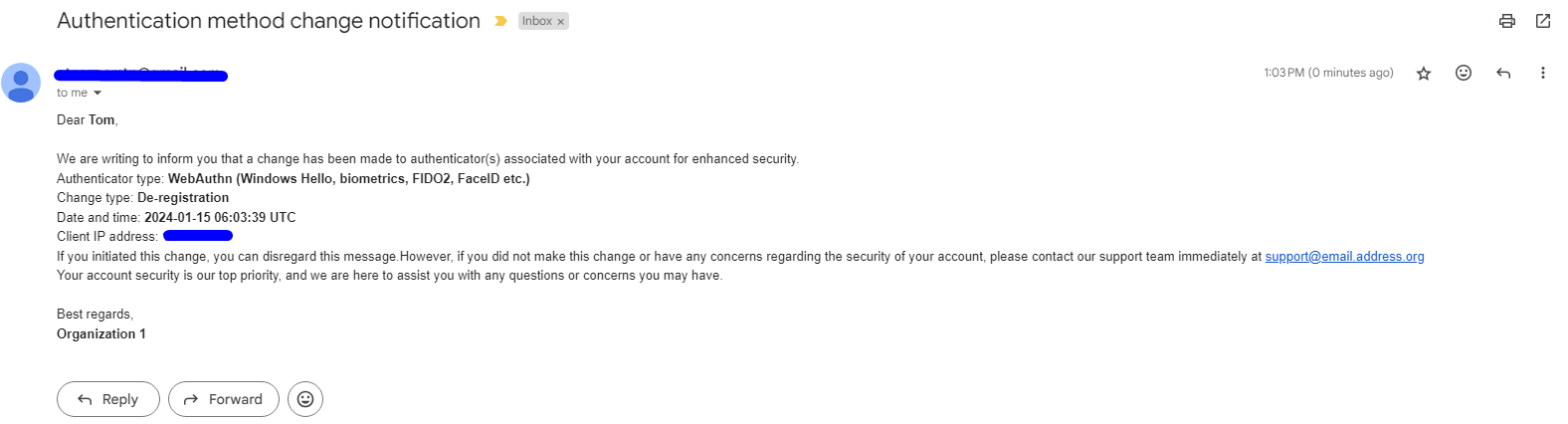
When a user deregisters a WebAuthn or an administrator resets it, a notification email will be sent to their mailbox.
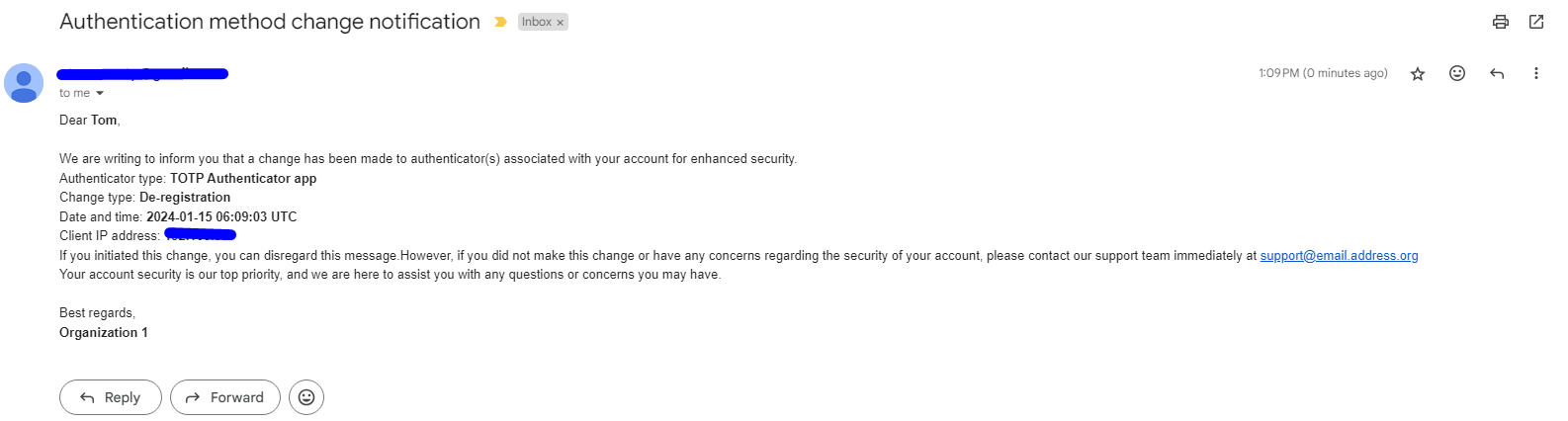
When a user deregisters a TOTP Authenticator or an administrator resets it, a notification email will be sent to their mailbox.
When a user deregisters a Device Registration (Trusted Browser) or an administrator resets it, a notification email will be sent to their mailbox.
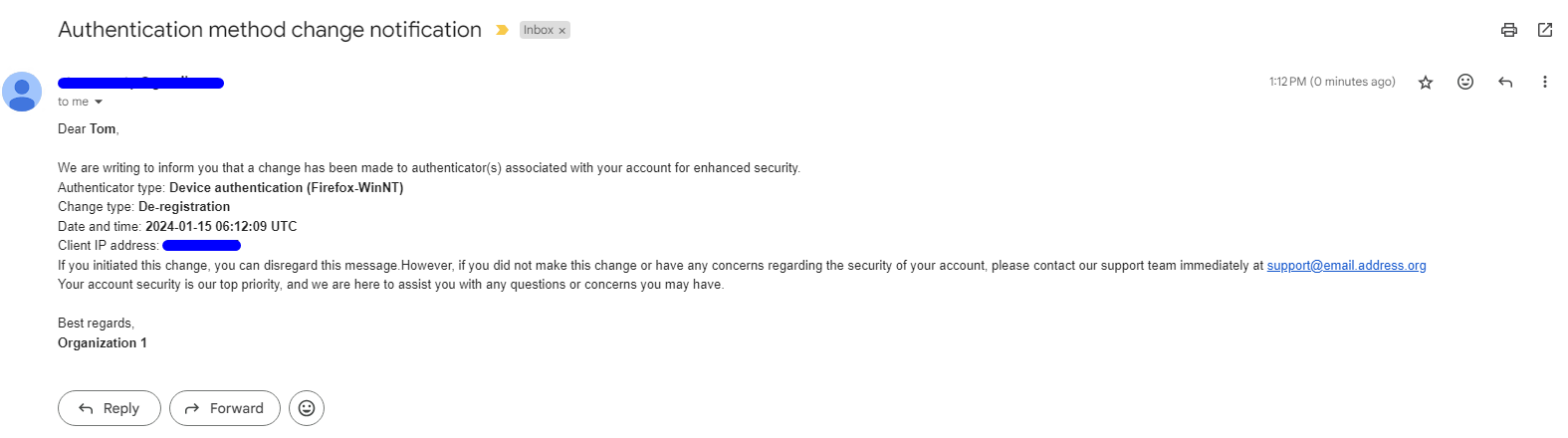
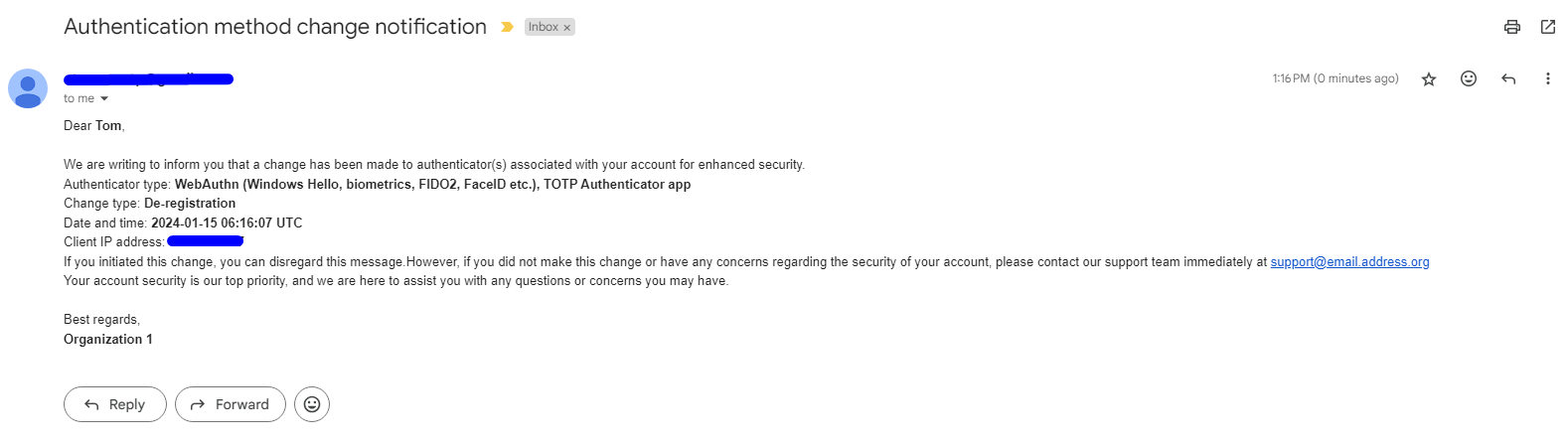
When an administrator clicks the Reset MFA methods button on Identify Admin to reset all MFA methods for a user, including a TOTP Authenticator, a WebAuthn, and a Device Authentication (Firefox), notification emails will be sent to their mailbox as follows:
When a user logs in using a recovery code of WebAuthn, a notification email will be sent to their mailbox.
When a user logs in using a recovery code of TOTP Authenticator, a notification email will be sent to their mailbox.
Notification via message bus
Configuration
Configure your Azure message bus or RabbitMQ queue in the Integration.
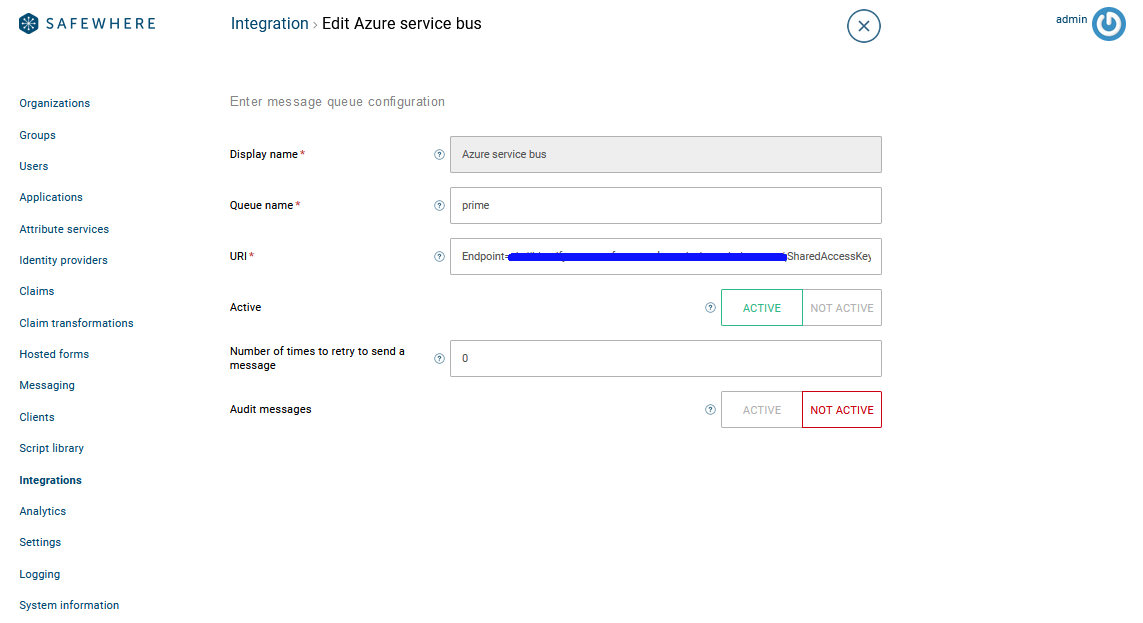
You can refer section How to use the domain event feature in this link for more detail.
Supported events
- When a user changes their password or an administrator changes it for them, the event below is published.
MessageID: 559c7e7eb84747089b2a784339374dff
CorrelationId: 0f72ed8a-ddd1-41ad-874f-70ff743b8f5a
MessageType: PasswordUpdated
AppId: ADMIN
MessageJson: {"Id":"25f04788-22d5-4391-8554-de877942b7a9","NewPassword":"********","MessageType":"PasswordUpdated"}
- When a user registers a TOTP Authenticator, WebAuthn or Device Authentication, the event below is published.
MessageID: e482196680a44521b80d2e58b9987645
CorrelationId: 00b1765a-d07b-40f9-aabc-fb59220878d0
MessageType: Created
AppId: ADMIN
MessageJson: {"UserSecondFactorCode":{"Id":0,"UserId":"d1ab4510-713c-474d-b816-63d0f64db369","OtpConnectionId":"759e00fe-ca07-46cd-8c62-bd76c8be4c72","OtpType":3,"IsEncrypted":false,"SecretCode":"********","RecoveryCode":"Kg=="}}
- When a user logs in using their recovery code, the event below is published.
**Message**
MessageID: 49c8763d26824e12aa634654400cf168
CorrelationId: b2a544e5-971b-4d92-af0e-e03682764ca3
MessageType: Updated
AppId: RUNTIME
MessageJson: {"Current":{"Id":25,"UserId":"f97f6f28-169c-4d9f-8970-d311dffd6e6e","OtpConnectionId":"13305aa3-0a84-430d-85d7-96b872f303b5","OtpType":5,"IsEncrypted":true,"SecretCode":"********","RecoveryCode":"Kg=="},"Previous":{"Id":25,"UserId":"f97f6f28-169c-4d9f-8970-d311dffd6e6e","OtpConnectionId":"13305aa3-0a84-430d-85d7-96b872f303b5","OtpType":5,"IsEncrypted":true,"SecretCode":"********","RecoveryCode":"Kg=="},"MessageType":"Updated"}
- When a user deregisters a TOTP Authenticator or WebAuthn from their account or an administrator resets a TOTP Authenticator, WebAuthn or Device Registration of the user, the event below is published.
MessageID: 351cd87cf68445bfaa10038f80cc0a22
CorrelationId: 7ff19097-5cd7-4214-b4b4-48b0fff44a17
MessageType: Deleted
AppId: ADMIN
MessageJson: {"UserSecondFactorCodes":[{"Id":1,"UserId":"d1ab4510-713c-474d-b816-63d0f64db369","OtpConnectionId":"759e00fe-ca07-46cd-8c62-bd76c8be4c72","OtpType":3,"IsEncrypted":false,"SecretCode":"********","RecoveryCode":"Kg=="}]}
- When an administrator clicks the Reset MFA methods button on Identify Admin to reset all MFA methods for a user, including a TOTP Authenticator, a WebAuthn, and a Device Authentication (Firefox), the following events are published:
**Message**
MessageID: 12a829dece7a4d93adb70d20e7b36bff
CorrelationId: 0490ac42-5260-42ca-b62f-2abb5ea9882a
MessageType: Deleted
AppId: ADMIN
MessageJson: {"UserSecondFactorCodes":[{"Id":32,"UserId":"f97f6f28-169c-4d9f-8970-d311dffd6e6e","OtpConnectionId":"13305aa3-0a84-430d-85d7-96b872f303b5","OtpType":6,"IsEncrypted":true,"SecretCode":"********","RecoveryCode":"Kg=="},{"Id":33,"UserId":"f97f6f28-169c-4d9f-8970-d311dffd6e6e","OtpConnectionId":"13305aa3-0a84-430d-85d7-96b872f303b5","OtpType":5,"IsEncrypted":true,"SecretCode":"********","RecoveryCode":"Kg=="},{"Id":34,"UserId":"f97f6f28-169c-4d9f-8970-d311dffd6e6e","OtpConnectionId":"13305aa3-0a84-430d-85d7-96b872f303b5","OtpType":3,"IsEncrypted":true,"SecretCode":"********","RecoveryCode":"Kg=="}]}
**Message**
MessageID: fad2cbd5164c4919a205e5f59dc4b08f
CorrelationId: 0490ac42-5260-42ca-b62f-2abb5ea9882a
MessageType: Deleted
AppId: ADMIN
MessageJson: {"UserSecondFactorDeviceRegistrations":[{"Id":6,"UserSecondFactorCodeId":32,"UserId":"f97f6f28-169c-4d9f-8970-d311dffd6e6e","OtpConnectionId":"13305aa3-0a84-430d-85d7-96b872f303b5","DeviceCookie":"********","DeviceName":"Firefox-WinNT","Type":1,"CreatedDate":"2024-01-10T04:41:25.117","LastAccessedDate":"2024-01-10T04:41:25.117"}]}