Safewhere Password Reset
Introduction
In this topic, we will show you how to set up a Password Reset site to reset Identify users' passwords. The use case is:
- A user forgets his or her Identify user's password.
- The user logs in to the Password Reset site using a NemID account.
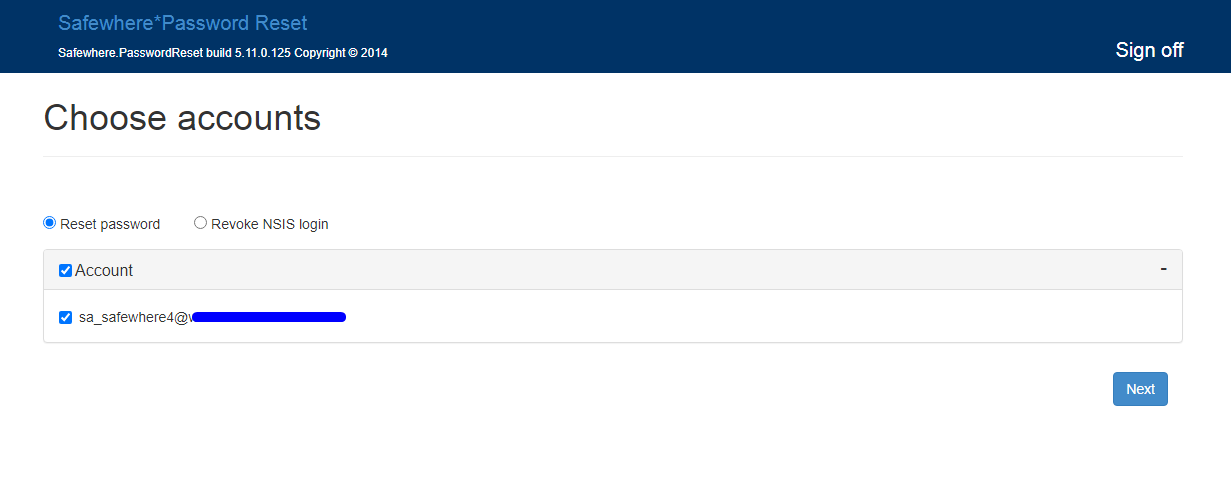
- The Password Reset site looks for users in Identify's database that match the NemID login and offers the user options to reset those accounts' passwords or disable them (aka to revoke the login option).
Installation
Identify configuration
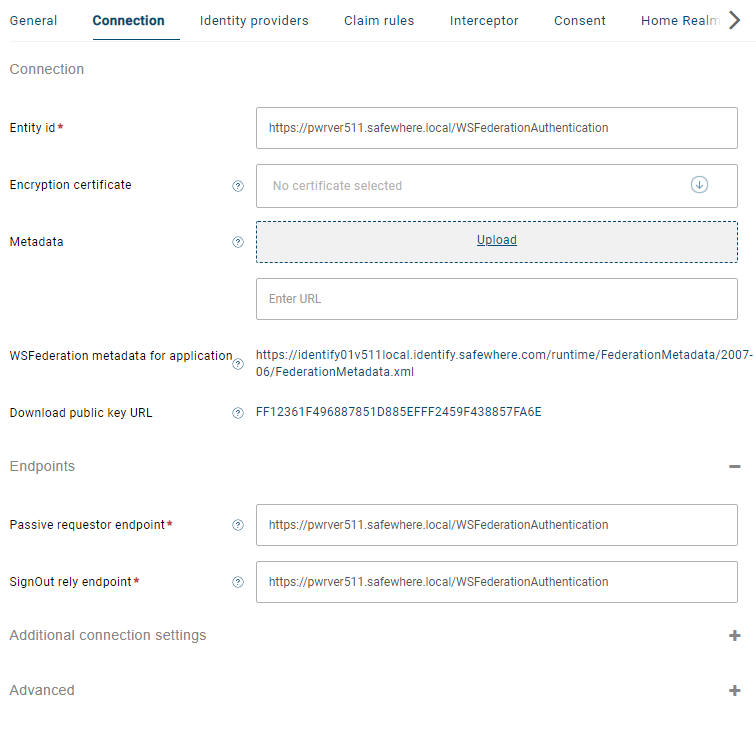
- Create a WS Federation application for Password reset site, and set the below values:
- Entity id: Enter
https://[PWRapplicationid]/WSFederationAuthentication - Passive requestor endpoint: Enter
https://[PWRapplicationid]/WSFederationAuthentication - SignOut reply endpoint: Enter
https://[PWRapplicationid]/WSFederationAuthentication - Encrypt certificate: Choose the encryption certificate that the Password Reset application uses.
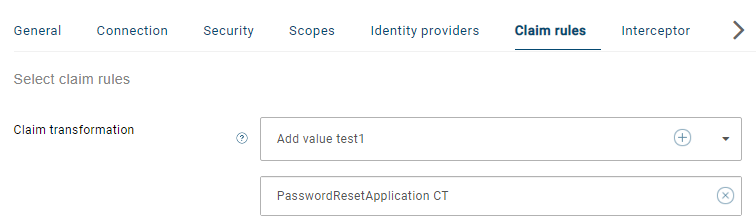
You need to prepare a claim transformation that can issue necessary claims. This example uses an Add value transformation.
- urn:internal:userid: enter an Identify user's id.
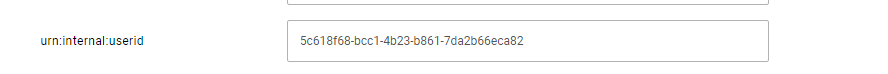
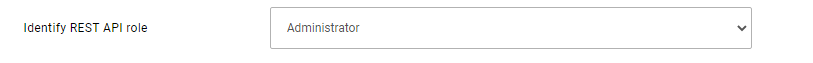
- urn:identify:rest-api:role: The friendly name is Identify REST API role. Add the Administrator option.
- urn:internal:userid: enter an Identify user's id.
Next, you need to create an OAuth 2.0 application for the Password Reset application to request Identify's access tokens. Open the connection to configure it:
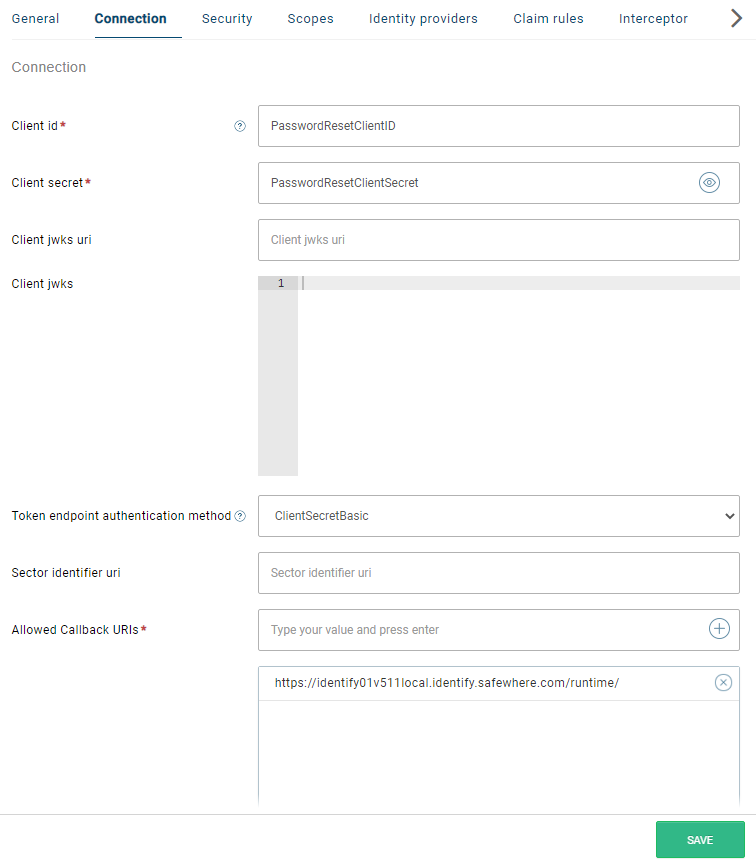
On the Connection tab:
- Client ID: Enter the unique ID of the application. Client ID is case-sensitive.
- Client secret: Enter the Client secret of the application. Client secret is case-sensitive.
- Token endpoint authentication method: Select ClientSecretBasic.
- Allowed Callback URIs: Enter
https://[identifydomain]/runtime/. This value is not used. - Application name: Enter the name of the application.
- Security token audience: Enter the Entity ID of your Identify instance.
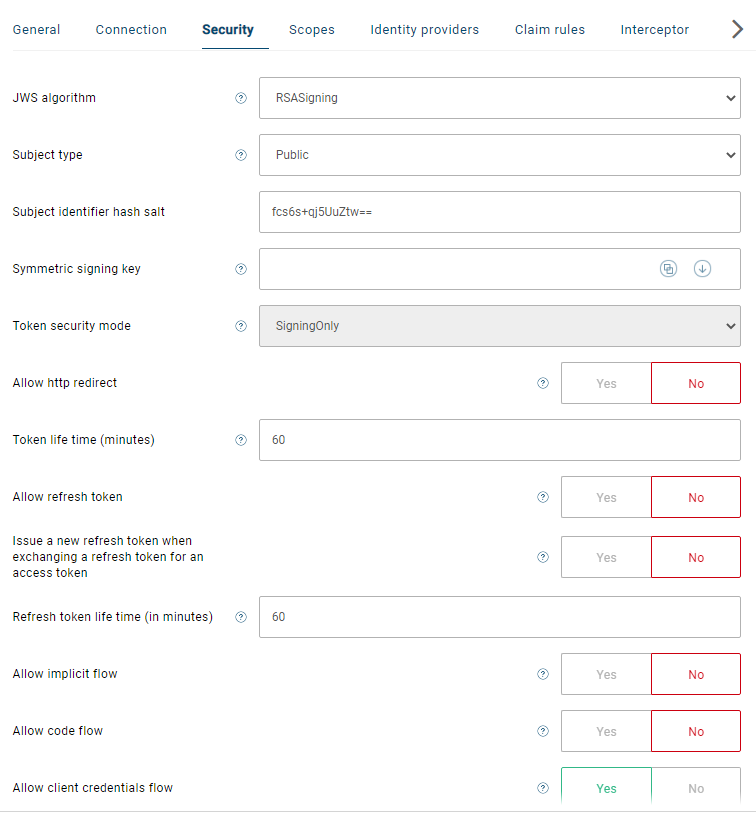
On the Security tab:
- JWS algorithm: Choose RSASigning.
- Symmetric signing key: You can leave it empty.
- Allow client credentials flow: Enable this setting to use the Client Credentials grant flow.
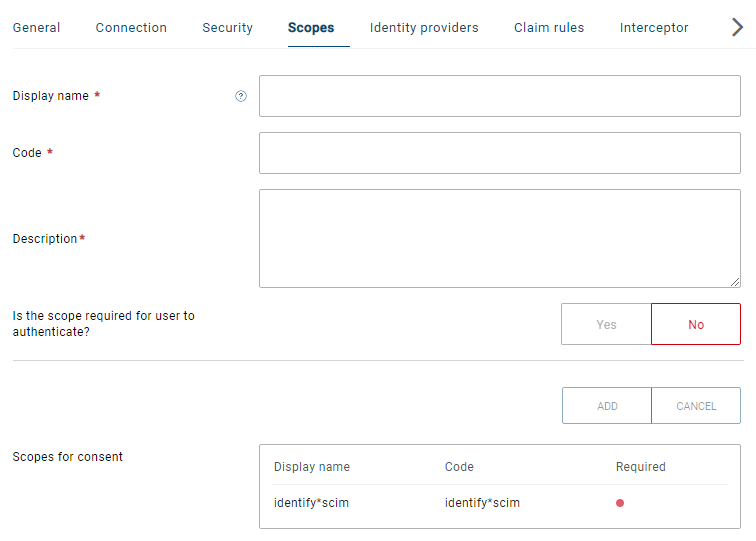
On the Scopes tab: Add the identify*scim scope
On the Claim rules tab: Add the claim transformation which you have created at the second step.
PasswordReset configuration
After installing the PasswordReset deployment package, you need to clone the folder
C:\Program Files\Safewhere\PasswordReset\WebAppto another location and rename its folder, e.g. toC:\inetpub\swpasswordresetOpen IIS and set up a new website that points to
C:\inetpub\swpasswordreset. In this sample, we use thepwrver511.safewhere.localdomain name.Add to the
hostfile:127.0.0.1 pwrver511.safewhere.localOpen to edit
C:\inetpub\swpasswordreset\web.configand update the CanRevokeLogin key to True.<add key="CanRevokeLogin" value="true" />and replace the placeholder texts:
- #AUDIENCE_URI#: Replace it with
https://[PWRapplicationid]/WSFederationAuthentication, e.ghttps://pwrver511.safewhere.local/WSFederationAuthentication - #TRUSTED_ISSUERS#: Replace it with thumbprint of the Identify's signing certificate.
- #WSFEDERATION_ISSUER#: Replace it with the Identify's WS-Federation protocol endpoint, for example,
https://identify01.identify.safewhere.com/runtime/WSFederation/WSFederation.idp - #WSFEDERATION_REQUIRED_HTTPS#: Replace it with the true value.
- #WSFEDERATION_CERTIFICATE_THUMBPRINT#: Replace it with the thumbprint of the encryption certificate that the Password Reset application uses.
- #AUDIENCE_URI#: Replace it with
Here is a sample after all the placeholder texts are corrected:
<system.identityModel>
<identityConfiguration>
<audienceUris>
<add value="https://pwrver511.safewhere.local/WSFederationAuthentication" />
</audienceUris>
<issuerNameRegistry type="System.IdentityModel.Tokens.ConfigurationBasedIssuerNameRegistry, System.IdentityModel, Version=4.0.0.0, Culture=neutral, PublicKeyToken=B77A5C561934E089">
<trustedIssuers>
<add thumbprint="3C1FD735A4035E3B78D33444DE5327C393AA282E" name="CN=IdentifyDefaultSigning, OU=Dev, O=Safewhere, L=Dev Bunker, S=Copenhagen, C=DK" />
<add thumbprint="FF12361F496887851D885EFFF2459F438857FA6E" name="CN=IdentifyTenantDefaultSigning, OU=Dev, O=Safewhere, L=Dev Bunker, S=Copenhagen, C=DK" />
</trustedIssuers>
</issuerNameRegistry>
</identityConfiguration>
</system.identityModel>
<system.identityModel.services>
<federationConfiguration>
<wsFederation passiveRedirectEnabled="true" issuer="https://identify01.identify.safewhere.com/runtime/WSFederation/WSFederation.idp" realm="https://pwrver511.safewhere.local/WSFederationAuthentication" requireHttps="true"/>
<cookieHandler requireSsl="true" />
<serviceCertificate>
<certificateReference x509FindType="FindByThumbprint" findValue="3C1FD735A4035E3B78D33444DE5327C393AA282E" storeLocation="LocalMachine" storeName="My" />
</serviceCertificate>
</federationConfiguration>
</system.identityModel.services>
- Edit
C:\inetpub\swpasswordreset\WindsorServices.configto remove the line:
<include uri="file://LdapTargetSystemPlugin.config" />
and enable:
<include uri="file://IdentifyTargetSystemPlugin.config" />
- Edit
C:\inetpub\swpasswordreset\IdentifyTargetSystemPlugin.configto add the component under the <components>-section:
<component service="Safewhere.PasswordReset.Infrastructure.ITargetSystem, Safewhere.PasswordReset.Infrastructure" type="Safewhere.PasswordReset.IdentifyLocalDb.IdentifyLocalDBTargetSystem, Safewhere.PasswordReset.IdentifyLocalDb" lifestyle="perWebRequest" id="swidentifyuser">
<parameters>
<id>swidentifyuser</id>
<name>swidentifyuser</name>
<configFile>C:\inetpub\swpasswordreset\App_Data\identify_targetsystem_passwordreset.config</configFile>
</parameters>
</component>
where the config file points to the location of the file identify_targetsystem_passwordreset.config
- Edit
C:\inetpub\swpasswordreset\App_Data\identify_targetsystem_passwordreset.configto update its content:
- Replace all appearances of
eid-test.safewhere.localwith the Entity ID of the configured Identify instance. - Replace values of the <ClientSecret>-section and the <ClientId>-section by the ones that you have entered to the OAuth 2.0 application.
- Replace the value of the <EmailClaimType>-section with the Identity bearing claim. In this sample, we use the http://schemas.xmlsoap.org/ws/2005/05/identity/claims/name claim type.
- Update the value of the <Timeout>-section to 60.
- Update the whole <property-filter>-section by
<property-filter />
- Replace the value of the <expression>-section, the <complexity-requirements>-section, and the <message>-section under the <password-policy>-section with the Identify's pasword policy Regex and its message text.
<expression><![CDATA[^(?=.*?\d)(?=.*[a-z])(?=.*[A-Z])(\w|[!@#$%^&*(\)\\\-=_+{}[\]|<>,./?~`:;'"]){8,100}$]]></expression>
<complexity-requirements>False</complexity-requirements>
<message><![CDATA[A valid password must have from 8-100 characters. In addition, it must not contain username but must contain at least 1 upper, 1 lower alphanumeric character, 1 digit and only those special characters are allowed !@#$%^&*()-=_+{}[]|\<>,./?~`:;'"]]></message>
- Update the error message of the
Password_Requirement1key found in theC:\inetpub\swpasswordreset\App_GlobalResources\PasswordReset.resxfile:
<data name="Password_Requirement1" xml:space="preserve">
<value><![CDATA[A valid password must have from 8-100 characters. In addition, it must not contain username but must contain at least 1 upper, 1 lower alphanumeric character, 1 digit and only those special characters are allowed !@#$%^&*()-=_+{}[]|\<>,./?~`:;'"]]></value>
</data>
and C:\inetpub\swpasswordreset\App_GlobalResources\PasswordReset.da.resx:
<data name="Password_Requirement1" xml:space="preserve">
<value><![CDATA[En gyldig adgangskode skal indeholde fra 8-100 tegn. Derudover må det ikke indeholde brugernavn, men skal indeholde mindst 1 stort bogstav, 1 lille bogstav, 1 ciffer, og kun de tilladte specialtegn !@#$%^&*()-=_+{}[]|\<>,./?~`:;'"]]></value>
</data>
Use the Password Reset site
After installation is done, you can open your browser to access the Password Reset site. After you log in using NemID, you can choose to reset your password or revoke your login.